I have to continue my post from last week about notPetya because I found new juicy information. An article in the Verge points to a blog that has, in my opinion, made a number of entities look not so expert (<= my attempt at being PC).
First, in the process of further researching the Verge article, I stumbled upon this blog: Weapons Grade Shenanigans. It is an excellent source of information and it provides a couple good laughs in the process. Such as this:
A Note on Analysis
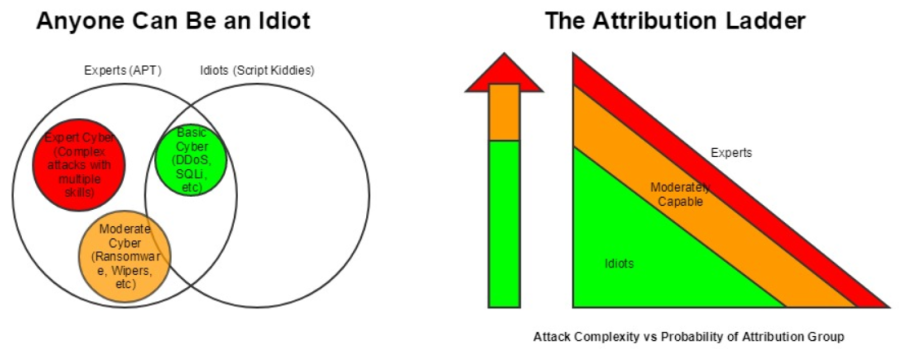
It is relatively simple for a complex adversary to pretend to be an idiot, and it is impossible for an idiot to pretend to be a complex adversary. Due to this immutable fact, it is always good to start with the premise that the hacker you’re analyzing is an idiot. When facts demonstrate this premise to be false, revise the analysis up the food chain until you’ve found a sufficiently complex level of capability to fit the facts. To do otherwise invites trouble for the analyst and the organizations they support. Since all attacks done by idiots can also be done by experts, any analysis which presupposes that the attackers are experts becomes fallacious on its face. You cannot DISPROVE an attack was done by a professional, you can only prove that a professional must have done an attack. A begets B, but B does not always beget A.
Port 21 – ProFTPD Version 1.3.4c
Port 22 – OpenSSH Version 5.4p1
Port 80 – ngnix Version 1.2.7
I will not repeat the details here, but these are old versions that have VERY known vulnerabilities. If fact the author states: … the trivial nature of this attack is such that any hacker with rudimentary capabilities could exploit it if the mod_copy was enabled. With trivial access to write to the hard drive, a rudimentary hacker could re-write files without difficulty. (in relation to the ProFTPD version) What is so special about the server at 92.60.184.55? It provides updates to M.E.Doc Doc accounting software, the most widely used for the delivery of regulatory reporting. Here is more information:
Ukrainian Cyber Police have published that at about 10:30 am GMT Tuesday (27 July 2017) M.E.Doc software on client machines ran a routine automatic update. At that time, the service EZVit.exe connected to address 92.60.184.55 with User Agent “medoc1001189” and downloaded 333 kilobytes of data (Source: https://www.facebook.com/cyberpoliceua/posts/536947343096100). This event was the initial virus download.
How did the clients download the updates?.. it was discovered that simply sending an HTTP GET request to 92.60.184.55 on port 80 with the User Agent “medoc1001189” will result in the server sending a “download” file. This strongly suggests that no authentication was/is required by M.E.Doc software to receive updates. It is probable that any file downloaded in this manner will be executed by the M.E.Doc auto-updater. In this manner, simply writing a virus to the download file may result in the execution of the virus on any M.E.Doc client machine.
I am starting to understand why in the US in some sectors there are regulations and heavy fines for non-compliance. As I have said in the past, you can blame the hackers, but a lot of the blame should be placed on organizations that let things like this happen.
No comments:
Post a Comment